Compliance - Addressing regulatory requirements
In today’s digital ecosystem, where threats loom larger and more complex than ever before, a robust cybersecurity strategy is no longer a luxury—it’s a necessity. Organizations are under increasing pressure to ensure their systems, data, and operations remain safe from cyber threats. Regulatory bodies have introduced a myriad of compliance requirements to guide companies on this path.
The importance of NIST compliance
NIST’s cybersecurity framework provides guidelines for organizations to manage and reduce cybersecurity risks. By categorizing cybersecurity outcomes into five functions: Identify, Protect, Detect, Respond, and Recover, NIST offers a roadmap for comprehensive security measures.
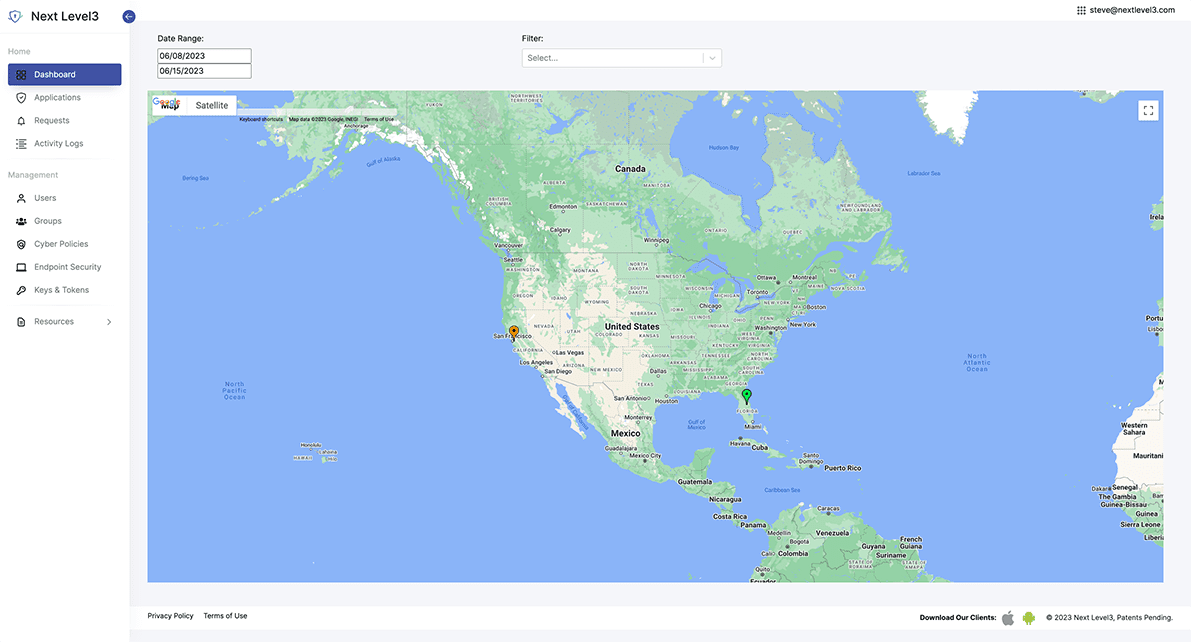
Next Level3’s suite of security solutions dovetails seamlessly with the NIST framework. From asset identification and threat protection to swift incident response, Next Level3 ensures each facet of the NIST recommendations is addressed.
Trusted by Insurance
80% of data breaches occur as a result of weak passwords or stolen credentials. Insurance companies are aware of this and are now mandating policyholders to implement MFA as a preventive measure against cyber attacks, reducing the risk of payouts on policies and ensuring profitability.
Get Compliance
Insurance companies require biometric Multi-Factor Authentication (MFA) as a mandatory security measure for obtaining cyber insurance.
Cost Reduction
Reduce the complexity of your MFA compliance, reduce help desk calls and gain visibility over endusers’ access to the organization’s assets are reasons for adopting passwordless authentication
Reduce Risk
By requiring passwordless biometric MFA for cyber insurance policies, insurance companies ensure that policyholders have the strongest possible security measures in place to minimize the risk of cyber threats.
Effective Security
Biometric MFA is considered the most secure method of MFA, as it uses unique physical characteristics such as fingerprints or facial recognition for authentication.
Mandates
80% of data breaches occur as a result of weak passwords or stolen credentials. Insurance companies are aware of this and are now mandating MFA compliance for policyholders as a preventive measure against cyber attacks, reducing the risk of payouts on policies and ensuring profitability.
Improved User Experience
Get a streamlined and better user experience and improve efficiency of your end users by adopting our passwordless authentication.
Enhanced authentication solutions for cyber insurance policyholders
Do your cyber insurance policy minimums address today’s most pressing threats? Social engineering, ransomware attacks, and business email compromises are amongst the biggest threats to cyber insurance policyholders.
Social engineering attacks
How it works:
Hackers use deception and manipulation to get someone to disclose information or data, taking an action that they would not normally do.
NL3’s solution:
When a breach is detected, trigger auto-lock account services or multi-approval policies to prevent someone from using credentials.
Ransomware/malware attacks
How it works:
Hackers use malware to encrypt files on a victim’s computer, causing extensive damage and making data inaccessible unless a ransom is paid.
NL3’s solution:
When a breach is detected, trigger alert-based policies to lock grouped accounts and prevent the spread of ransomware.
Business email compromise
How it works:
Hackers use an organization’s email system to send fraudulent messages and gain access to sensitive information or business secrets.
NL3’s solution:
If a change is attempted to initiate a wire fraud, NL3’s multi-approval policies can prevent someone from using credentials.
Automatic push attack aware protection without codes



Use your existing mobile or web FIDO2 supported devices




Why choose Next Level3?

JIT Access
Passwordless Identity seamlessly connected to your existing identity infrastructure.

JIT Policies
Redefine account control for your organization solving critical internal use cases.

JIT Approvals
Enable customized approvals for any application action preventing fraud and extending biometric protections into your application use cases.