Vulnerability Mitigation - Securing Entra and Outlook
In light of the emerging security issues, Microsoft is confronted with serious vulnerabilities in both its Outlook service (CVE-2023-23397) and Entra Active Directory (Azure AD). Discover how using JIT Access and PAM can prevent a variety of CVE’s and attacks.
Exploring the vulnerabilities
In light of the emerging security issues, Microsoft is confronted with serious vulnerabilities in both its Outlook service (CVE-2023-23397) and Entra Active Directory (Azure AD). Threat actors have exploited these vulnerabilities to carry out advanced cyber-attacks. This article delves into these vulnerabilities and how Next Level3 JIT Access and JIT Policies framework proactively mitigate these threats, leveraging Azure’s Protected Actions feature.
How our JIT Identity solutions solve the problem
Next Level3’s security solutions are designed to address and prevent vulnerabilities such as CVE-2023-23397 and Azure AD flaw. They focus on three core areas: enhancing security protocols, improving existing infrastructure, and promoting a proactive approach to identifying and mitigating threats.
Layering Security Protocols
By layering security protocols, Next Level3's products effectively respond to different stages of an attack. They prevent unauthorized access and swiftly detect and neutralize threats before they cause significant damage. In the event that one system is breached, the other acts a backup preventing access.
Entra's Protected Actions
Next Level3 takes a proactive approach to threat mitigation, a part of which involves leveraging Entra's new Protected Actions feature. This feature improves Conditional Access by targeting individual high-risk actions in the Entra AD Portal, providing a defense-in-depth approach, and delivering optimized security for highly sensitive operations.
Enhancing Existing Systems
The products integrate seamlessly into existing infrastructures, which enhances their ability to detect and respond to threats. This means they can work with Entra AD's identity and access management service, enhancing their capabilities to resist any threats associated with its vulnerabilities.
Using Protected Actions
Protected Actions, when properly implemented, can effectively prevent privileged operations from being exploited, providing an additional layer of protection. The feature can be applied to specific user actions executed within the Azure AD portal, including those involving modifications to access rights and multi-factor authentication configurations.
How Protected Actions Work
The implementation of Entra’s Protected Actions feature follows a three-step process:
- Preparation
This involves setting up ‘regular’ Conditional Access (CA) policies and migrating trusted IPs from the legacy MFA portal to ‘Named Locations’ in Entra (Azure AD). - Configuration
This step requires configuring Protected Actions and Conditional Access Rule, involving the creation of a new ‘Authentication Context’ and tagging the action with the Authentication Context. - Administrator Experience and Logging
This involves testing the behavior from the user who is included in the rule and has the ‘Conditional Access Administrator’ role. By using ‘Authentication Context’, ‘Protected Actions’, and ‘Conditional Access’, administrators can execute specific actions from a particular device or with a specific method.
Robust Defense
Next Level3’s products, combined with Entra’s new Protected Actions feature, form a robust defense mechanism to prevent the exploitation of vulnerabilities such as CVE-2023-23397 and the Entra AD flaw. These tools promote a proactive approach to security and offer comprehensive protection, ensuring the integrity and confidentiality of sensitive information and operations.
Automatic push attack aware protection without codes



Use your existing mobile or web FIDO2 supported devices




Why choose Next Level3?

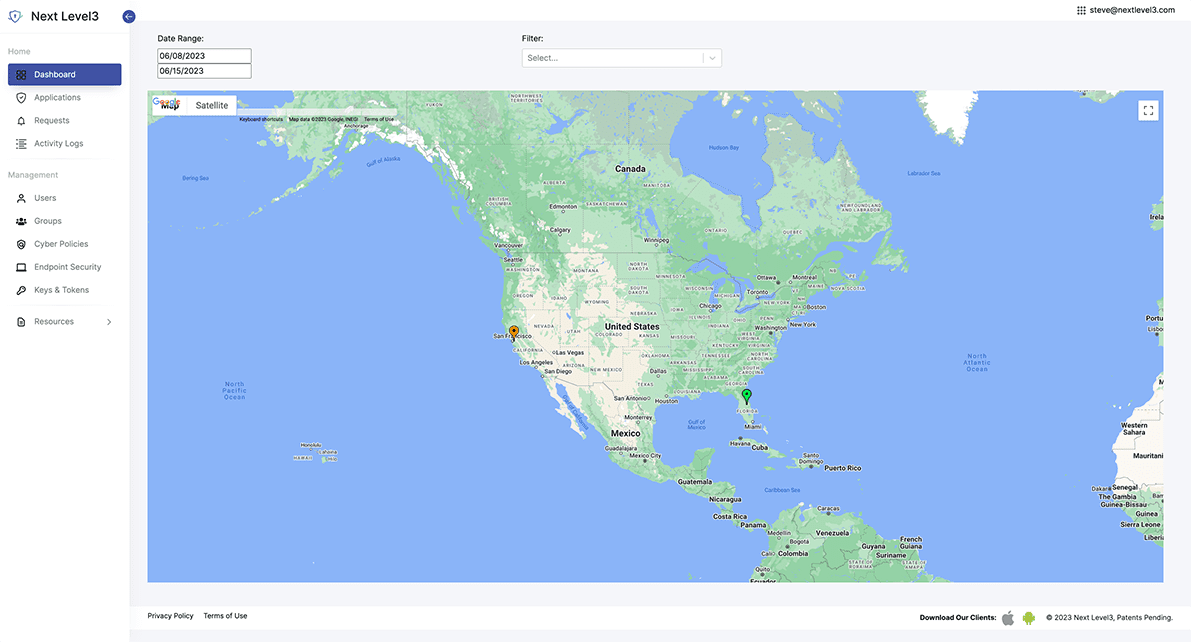
JIT Access
Passwordless Identity seamlessly connected to your existing identity infrastructure.

JIT Policies
Redefine account control for your organization solving critical internal use cases.

JIT Approvals
Enable customized approvals for any application action preventing fraud and extending biometric protections into your application use cases.